In the vast digital seas of our interconnected world, we continually face a storm of cybersecurity threats, notably the ever-evolving danger of malware. As these invisible threats grow more sophisticated, the need for stalwart defenses has become increasingly crucial.
Despite our most advanced antivirus software, the task of defending against this wave of malware remains an arduous and uphill battle. For professionals in cybersecurity, and particularly those working as Malware Analysts, their daily challenge is to identify, scrutinize, and understand the many forms of malware infiltrating our digital domains. This typically involves labor-intensive, manual processes using specialized tools such as IDA Pro, WinDbg, and OllyDbg, which can be time-consuming.
Faced with this relentless digital onslaught, how do we fortify our defenses and secure our virtual infrastructure? The answer lies in the extraordinary capabilities of machine learning.
Machine Learning: A Game-Changer in Malware Detection
In the intricate and unpredictable sphere of cybersecurity, numerous challenges lie in wait. However, amid these trials, one pioneering approach has emerged, showing considerable promise and potential for future applications: machine learning.
Rather than the conventional approach of painstakingly establishing a manual set of rules for malware detection, machine learning offers an intriguing alternative. This innovative methodology allows us to train a machine utilizing highly sophisticated algorithms.
In machine learning, algorithms act as decision-making guideposts. They operate by learning from previous experiences, or in this case, from pre-existing data. The machine is meticulously trained on a vast set of diverse and complex data, allowing it to learn, adapt, and make precise predictions on new, unseen data.
In the context of cybersecurity, the utility of this technique is exceptional. A machine learning-based system is capable of analyzing millions of system call characteristics in real time. The scale of this analysis far exceeds what human analysts could achieve, particularly given the speed and accuracy required.
Most notably, machine learning methods are not only confined to identifying known malware, but also they are equally proficient at determining whether a file is malicious or benign, even when encountering novel, previously unseen forms of malware.
Just as our immune system works tirelessly to identify and neutralize foreign invaders in our bodies, machine learning can act as an immune system for our digital environments, identifying and mitigating the threat of malware. Today, we’ll embark on a journey to explore the integration of machine learning and malware detection. Our primary aim is to guide anyone new to the field through this intriguing landscape.
The Essentials for performing Malware Analysis
To kick things off, it’s paramount that we equip ourselves with the right set of skills and tools needed for malware analysis. We will be relying on below libraries and languages.
- You must have basic knowledge and understanding of System calls and different machine learning classifier.
- These include NumPy for array processing.
- Pandas for data manipulation, and a machine learning algorithm to classify the dataset.
- For visualizations, we will use the Seaborn library.
- DataFrames for data manipulation.
- The project will be developed and presented in Jupyter Notebook and will utilize Vim as the text editor.
- To match patterns, we will be leveraging Regular Expressions, and Python will serve as our coding language.
Establishing a Safe Environment for Malware Analysis
Once above mentioned prerequires are in place, you’ll need to set up a secure testing environment for your malware. You can download and install the Linux system and Windows Virtual Machine on Oracle VM VirtualBox to run the Malware for testing purpose.
To begin with our malware analysis, it is crucial to build an isolated, controlled, and secure environment, often referred to as a ‘“lab”. In this context, “isolation” is key. The lab should be completely separated from your regular work environment to avoid any potential collateral damage. This isolation is established through a sandbox or virtual system, ensuring it employs Network Address Translation (NAT) and has no shared folders or USB connections. It’s also pivotal to keep all systems updated with the latest security patches.
Collection and Verification of Malware Samples and Legitimate Applications
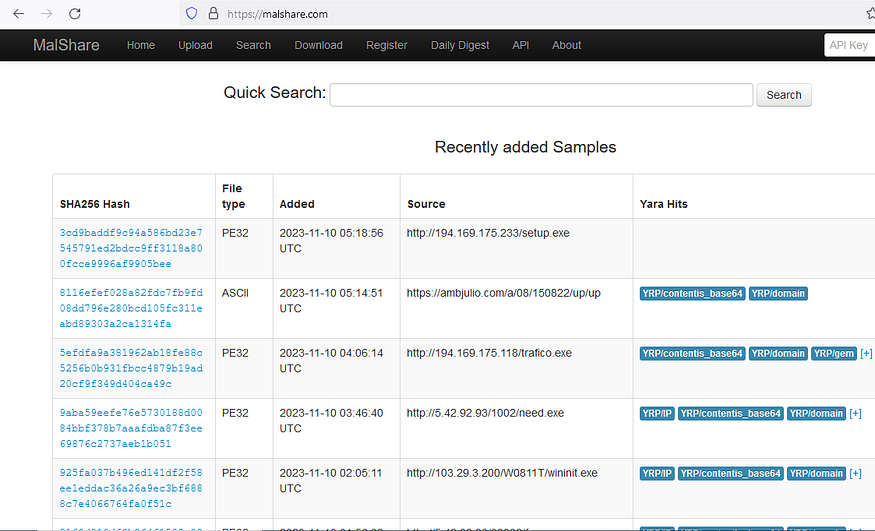
Our next step involves collecting malware samples from various repositories. We understand that navigating the complex world of cyber threats requires access to tangible examples and real-world scenarios. To this end, we’ve included below images in our article that lists the various sites we utilized to download malware samples for our work.

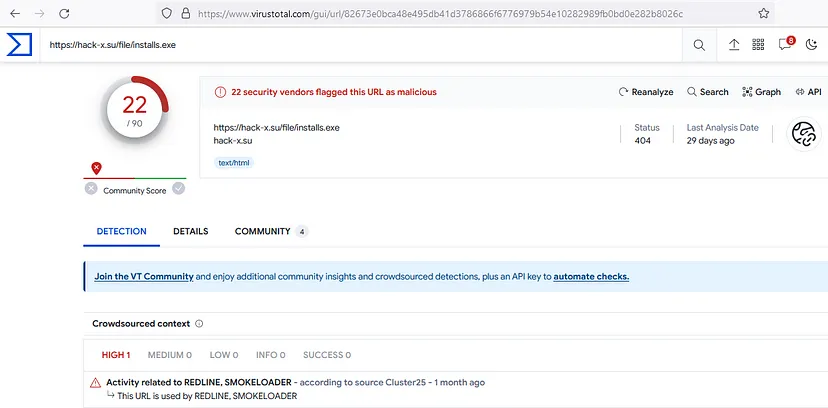
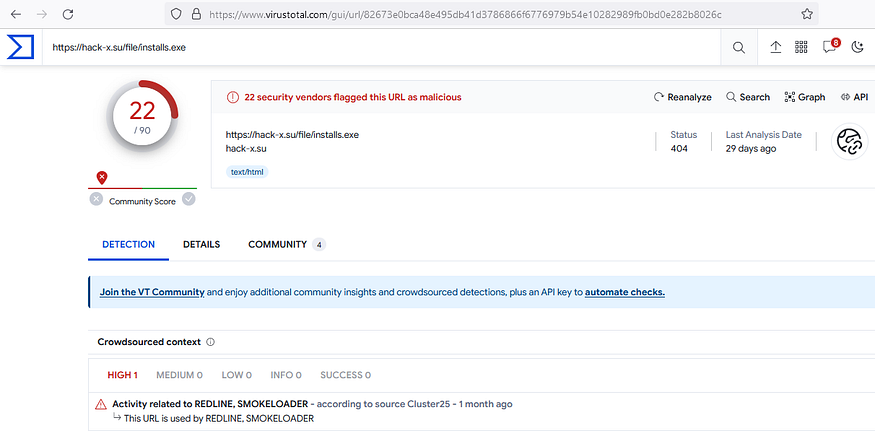
These samples serve as the fodder for our machine-learning model, allowing it to learn and adapt. To ensure that these files are indeed malware, they can be uploaded to Virus Total or similar platforms for verification as shown in the image below.
Regarding legitimate application samples, it can be downloaded directly from Microsoft’s official website or sourced from pre-installed Windows apps.
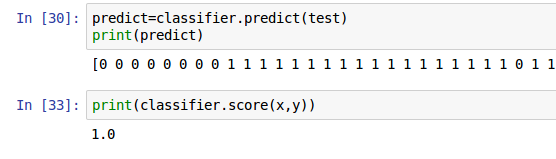
In the next part of this Blog, we will capture the system calls of the Malwares as well as legitimate applications, then, segregate them to train and test data set, after that, fine-tune them for our own machine learning classifier.